Trend Micro Cloud One – Open Source Security by Snyk
Visibility and monitoring of open source vulnerabilities for SecOps
Overview
Integrate and Protect
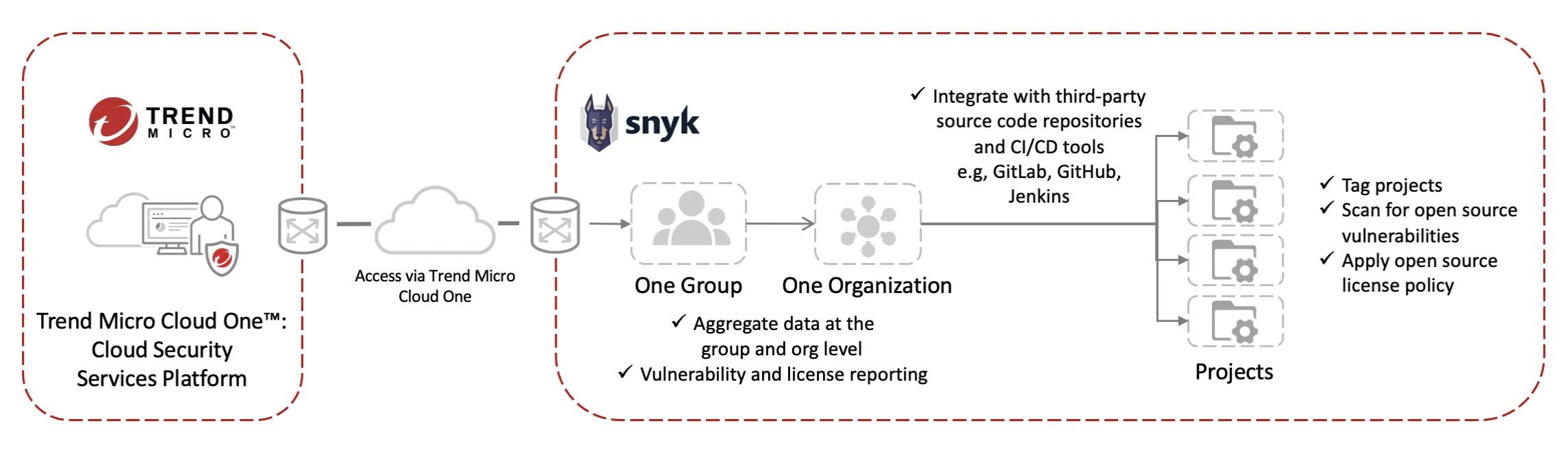
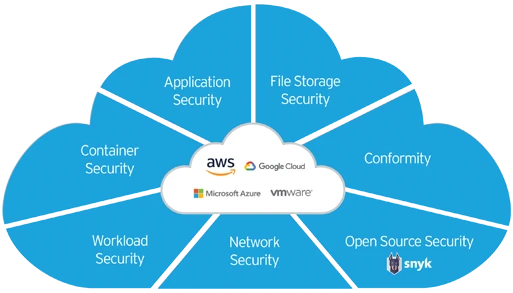
Trend Micro Cloud One - Open Source Security by Snyk automatically finds, prioritizes, and reports vulnerabilities and license risks in open source dependencies used by your applications. As part of the Trend Micro Cloud One™ security platform, Trend Micro Cloud One – Open Source Security by Snyk connects with your code repositories and CI/CD pipelines to scan projects. This enables security teams to gain more relevant insights and improve risk management thanks to increased visibility, tracking, and early awareness into open source issues.
Seamless and Fast
Built right into the service console, you can easily add your source code repositories to provide instant results of scanned projects and pertinent indirect dependency information. This allows security teams to be able to see across the entire software supply chain in order to promptly understand open source vulnerabilities and receive remediation insights and tracking all from one console. Furthermore, Trend Micro Cloud One - Open Source Security by Snyk automatically identifies as well allows you to search for open source license risks that could possibly affect your company’s legal requirements and digital property.
Uncover vulnerabilities
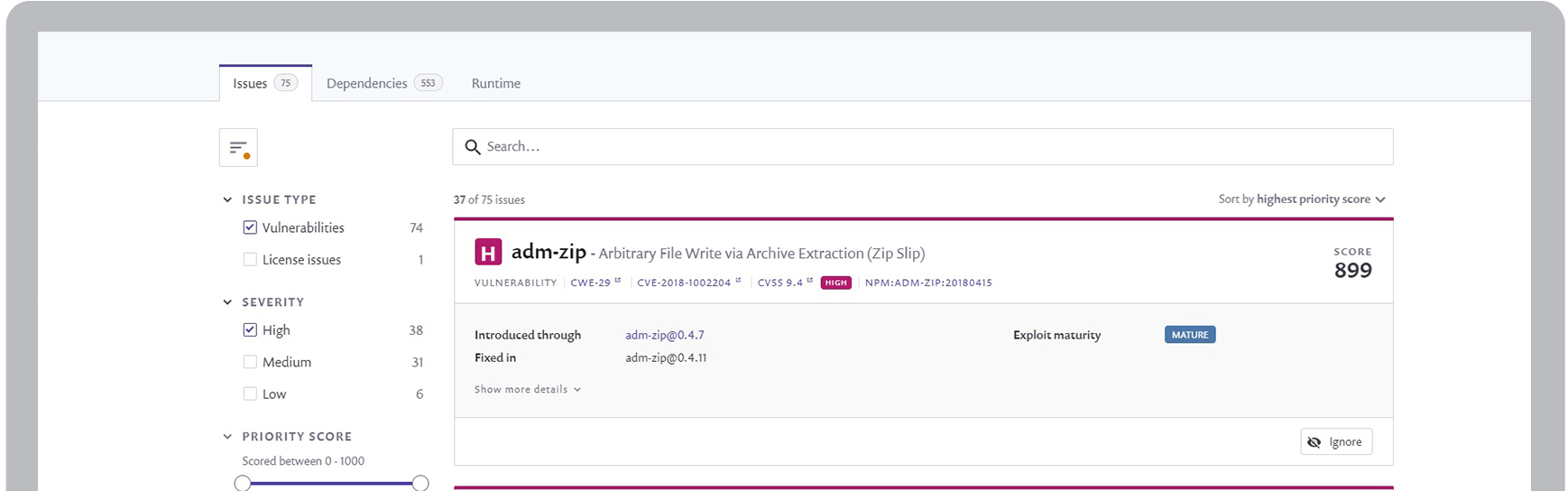
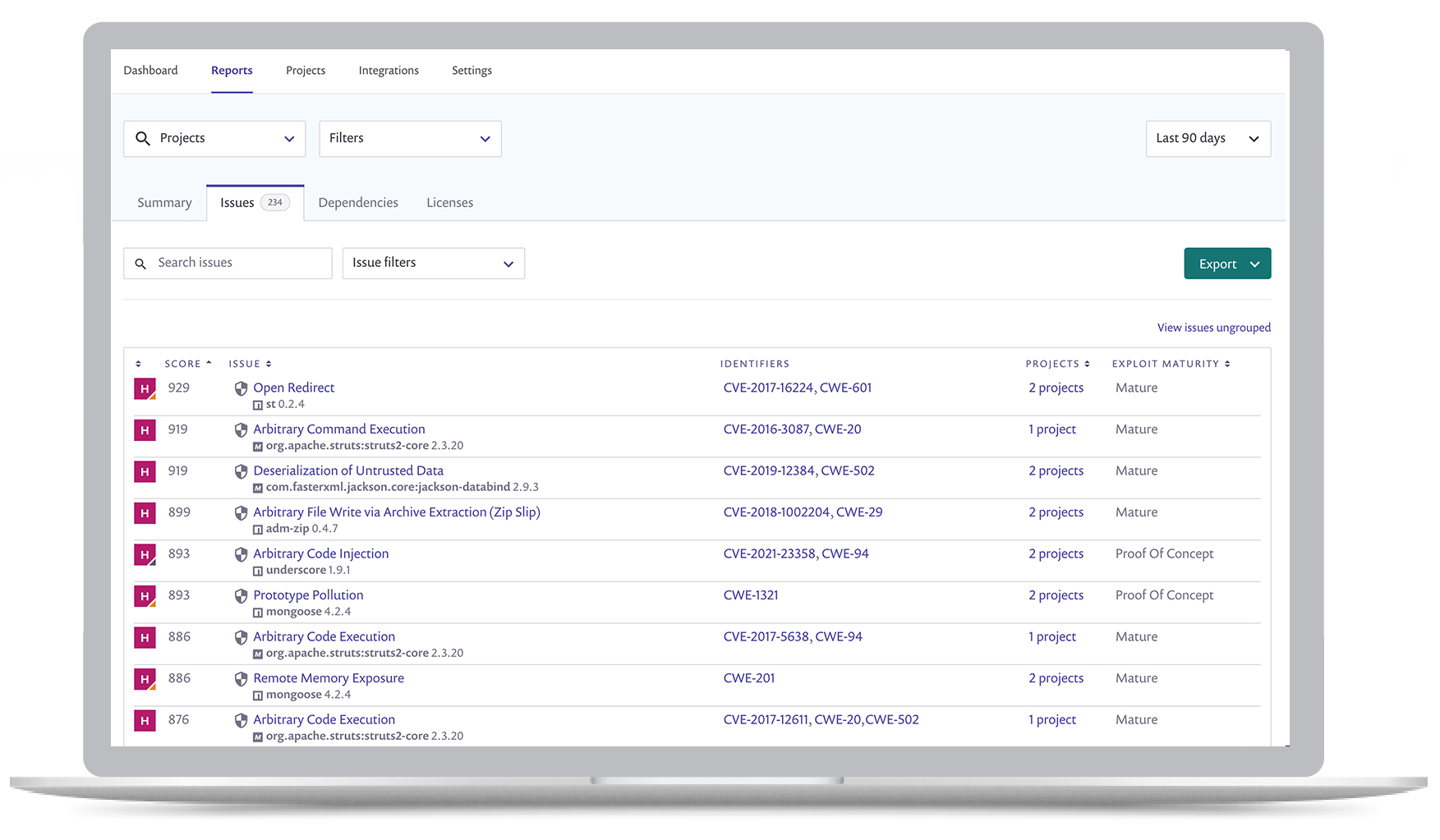
Empower security operations teams to identify open source code vulnerabilities and license risks across application components for enhanced visibility. Surface rich intelligence about indirect dependencies that are impacting your software bill of materials and security.
Improve visibility
Imagine having the early advantage of understanding open source risks within application development streams. Together, Trend Micro and Snyk have made this a reality through the Trend Micro Cloud One SaaS security platform for cloud builders
Prioritize risks
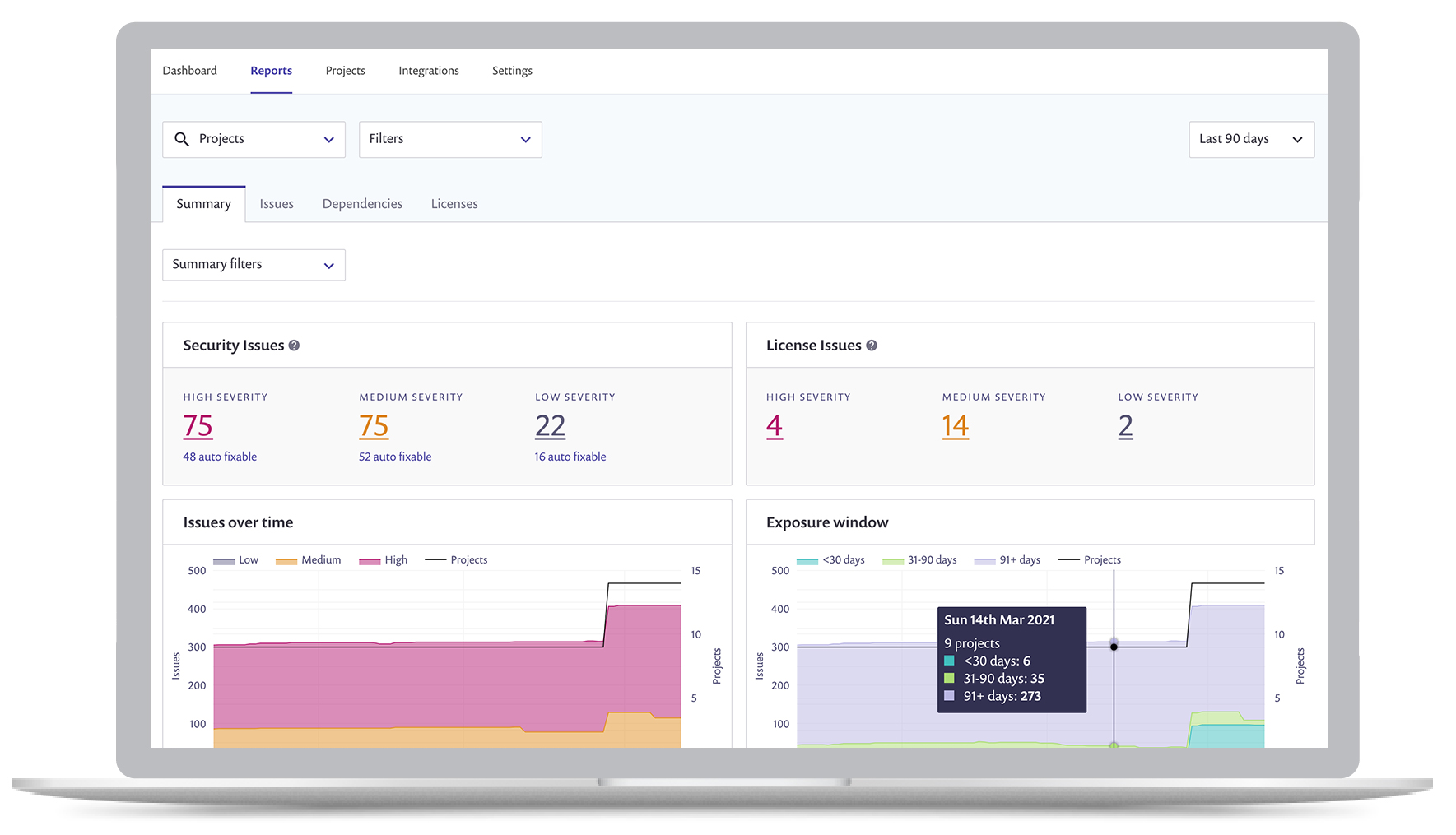
Manage open source vulnerabilities introduced during application development in an efficient and easy to implement security workflow. Balance business velocity with immediate risk awareness by monitoring trends and prioritizing issues found in open source dependencies.
Informative and Trackable
- Scan projects in code repositories to provide security teams with visibility into open source dependency vulnerabilities.
- Monitor trends across the entire organization’s open source landscape through dashboards and reports.
- Visibility of all dependency paths to identify vulnerabilities that development teams may be unaware of.
- Receive explicit step-by-step instructions from the Knowledge Base to remediate risks.
- Eliminate a large blind spot for security teams via more insights into fast pace development cycles
Why you need it
- 80% of application code is open source
- 2.5x increase in open source vulnerabilities in the last 3 years
- 78% of vulnerabilities are found in in-direct dependencies